
Author: CyberDudeBivash
Powered by: CyberDudeBivash Brand | cyberdudebivash.com
Related:cyberbivash.blogspot.com
Daily Threat Intel by CyberDudeBivash
Zero-days, exploit breakdowns, IOCs, detection rules & mitigation playbooks.
Follow on LinkedInApps & Security ToolsCYBERDUDEBIVASH CYBERDUDEBIVASH PVT LTD WWW.CYBERDUDEBIVASH.COM
When Malware Stops Looking the Same
Understanding Polymorphic Malware in 2026 & the CyberDudeBivash Countermeasure

5
January 2026
By Bivash Kumar Nayak
Founder & Cybersecurity Strategist, CyberDudeBivash Pvt. Ltd.
Introduction: The End of Static Malware
For years, defenders relied on a simple assumption:
malware looks the same every time it spreads.
That assumption no longer holds.
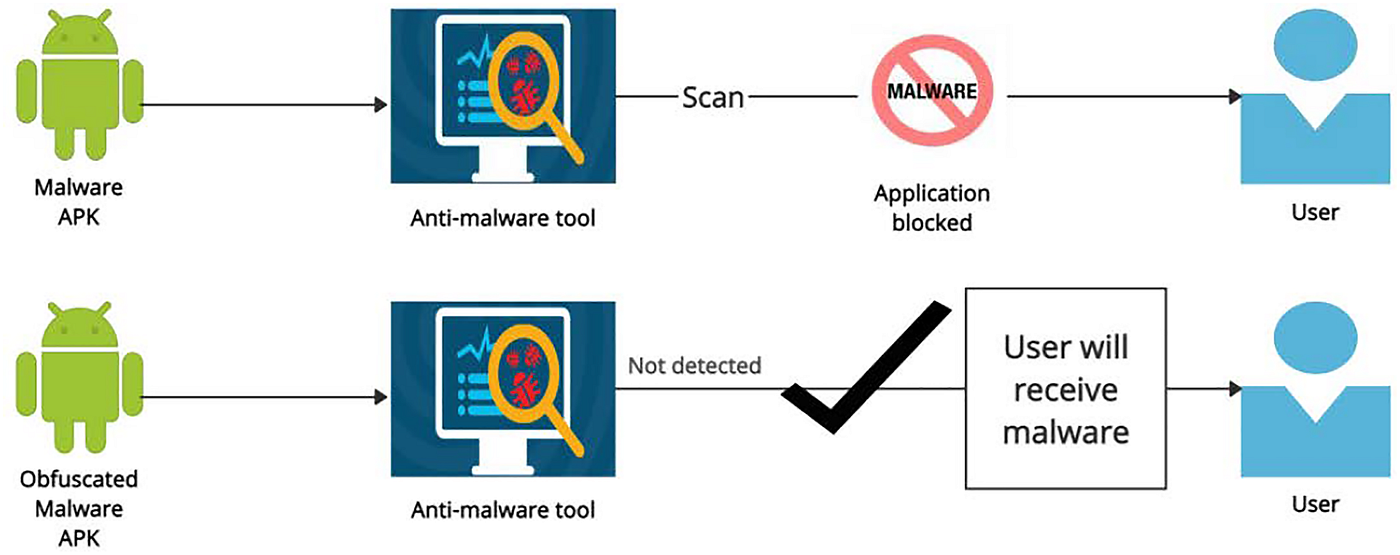
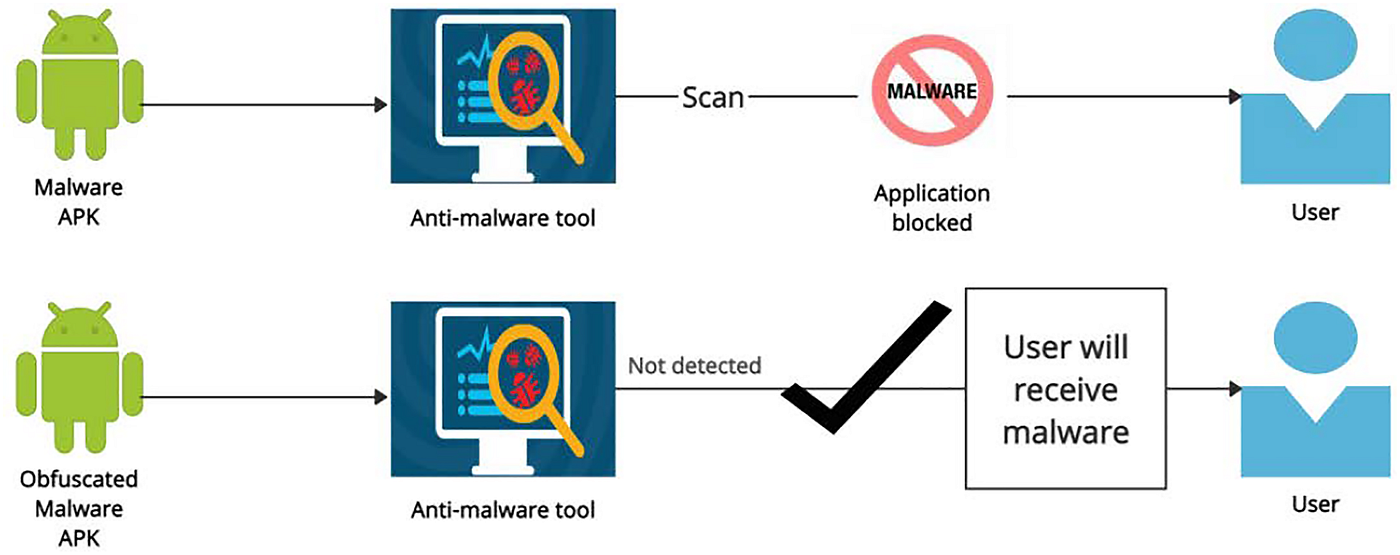
In 2026, modern malware families rarely reuse identical code. Instead, they continuously mutate their structure while preserving functionality — a technique broadly known as polymorphism. This evolution has rendered many signature-based and static detection mechanisms ineffective.
The result is a widening detection gap between how attackers operate and how defenders test their controls.
At CyberDudeBivash, we believe closing that gap starts with understanding evasion safely — not in the wild, but in controlled, ethical environments.
What Is Polymorphic Malware — and Why It Matters Now


4
Polymorphic malware refers to malicious software that changes its internal representation each time it is generated or delivered, while its behavior remains functionally identical.
Common Polymorphic Techniques Seen in 2026
- Variable and function renaming
- String encoding or encryption
- Dead code insertion
- Instruction reordering / line shuffling
- Minor logic restructuring
These techniques allow malware to:
- Evade hash-based detection
- Bypass static signatures
- Reduce the effectiveness of rule-based engines
- Force defenders to rely on behavior and context
Importantly, polymorphism itself is not malicious — it is a technique. The danger lies in how it is used.
The Defensive Blind Spot: How Teams Fall Behind
Most organizations still test their security controls using:
- Known malware samples
- Static indicators
- Limited test cases
This creates a dangerous illusion of coverage.
Attackers, meanwhile, generate hundreds or thousands of unique variants of the same payload — each slightly different, each capable of bypassing poorly generalized detection logic.
Without safe tooling to simulate this behavior, defenders are left asking:
“Would our detection still work if the code looked different?”
Why Ethical Simulation Is the Only Responsible Approach
Simulating polymorphism in live malware is not responsible and not necessary.
What defenders actually need is:
- Harmless code
- Structural mutation
- Controlled outputs
- Zero execution risk
- Clear visibility into how signatures break
This is the exact gap we set out to address.
Introducing CyberDudeBivash AI-Polymorphic Malware Simulator v2026.1


4
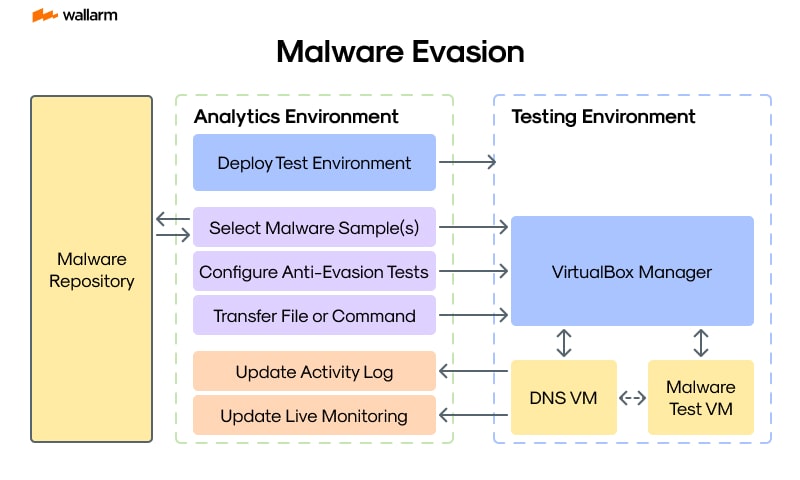
To help security teams study polymorphism without creating threats, we’ve released:
CyberDudeBivash AI-Polymorphic Malware Simulator v2026.1
An ethical, zero-execution red-team research tool that generates polymorphic variants of harmless input code — enabling defenders to test detection resilience safely.
This is not a malware builder.
It is a defensive research instrument.
What the Simulator Does (Safely & Transparently)
Structural Code Mutation
The simulator applies controlled transformations such as:
- Variable renaming
- String obfuscation
- Dead-code injection
- Line and block shuffling
Each output is functionally equivalent but structurally distinct.
Batch Variant Generation
Generate multiple variants from a single input to:
- Stress-test detection logic
- Observe false negatives
- Evaluate rule generalization
Diffs are generated to show exactly what changed.
Reporting for Analysis
The tool produces:
- JSON reports for automation
- HTML reports for human analysis
This makes it suitable for:
- Red-team exercises
- Blue-team tuning
- Security engineering reviews
- Training and education
Zero-Execution Safety by Design
The simulator:
- Does not execute code
- Accepts harmless samples only
- Runs fully offline
- Contains no payload logic
- Makes no external network calls
Every design decision follows zero-trust secure coding principles.
Who This Tool Is For
This simulator is designed for:
- Red teams validating EDR resilience
- Blue teams improving detection logic
- Malware analysts studying evasion patterns
- Security engineers tuning signatures
- Researchers and educators teaching modern threats
It is not intended for offensive deployment or misuse.
Availability & Access
Free Open-Source Edition
The full simulator is available under our official GitHub organization:
The open-source version includes:
- Core mutation engine
- Batch generation
- Diff analysis
- HTML & JSON reporting
Pro & Enterprise Editions (Coming Soon)
Advanced use cases will be supported through Pro editions, including:
- ML-driven mutation strategies
- Detection telemetry correlation
- Enterprise reporting
- Integration with lab environments
Pro / Enterprise inquiries:
iambivash@cyberdudebivash.com
Ethical Use Statement
This tool is provided strictly for authorized, defensive, and educational purposes.
Understanding how evasion works is essential to stopping it — but only when done responsibly, transparently, and within legal boundaries.
CyberDudeBivash does not support malicious activity.
Final Thoughts: Studying Evasion to Build Stronger Defenses
Polymorphic malware represents a shift in attacker mindset:
Detection avoidance is now continuous, automated, and adaptive.
Defenders must respond the same way — not with fear, but with knowledge and validation.
By safely simulating how structure changes break detection, teams can:
- Harden signatures
- Improve behavioral logic
- Reduce blind spots
- Build confidence in their controls
At CyberDudeBivash, our mission remains clear:
Turn attacker techniques into defender advantages — ethically and openly.
Your Cybersecurity Sentinel
Bivash Kumar Nayak
Founder, CyberDudeBivash Pvt. Ltd.
www.cyberdudebivash.com
https://github.com/cyberdudebivash
#CyberSecurity #MalwareAnalysis #Polymorphism #RedTeam #BlueTeam #EDR #ThreatResearch #CyberDudeBivash
Leave a comment