
Daily Threat Intel by CyberDudeBivash
Zero-days, exploit breakdowns, IOCs, detection rules & mitigation playbooks.
Follow on LinkedInApps & Security ToolsCYBERDUDEBIVASH CYBERDUDEBIVASH PVT LTD WWW.CYBERDUDEBIVASH.COM
Why ZTNA Misconfigurations Are the New Attack Surface — and How CyberDudeBivash Fixes It

5
January 2026
By Bivash Kumar Nayak
Founder & Cybersecurity Strategist, CyberDudeBivash Pvt. Ltd.
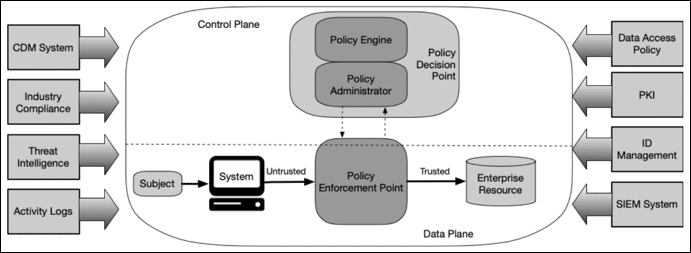
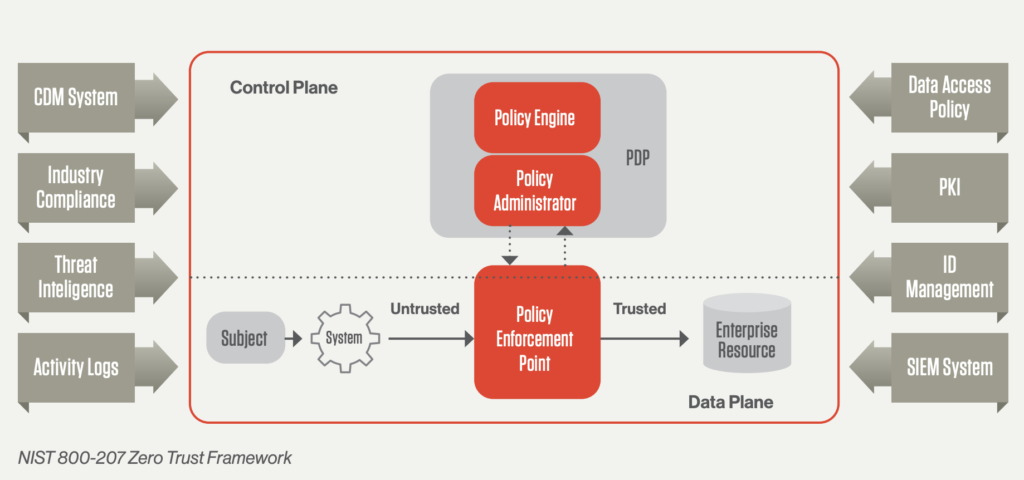
Introduction: Zero Trust Is Not Broken – Validation Is
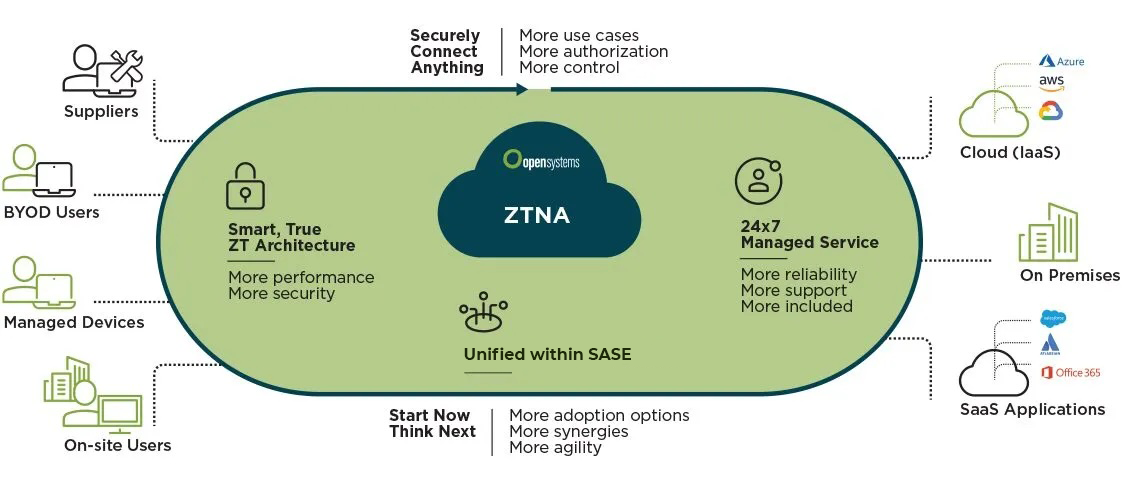
“Zero Trust” has become one of the most widely adopted security models of the last decade. Enterprises around the world have invested heavily in Zero-Trust Network Access (ZTNA) platforms to replace legacy VPNs and reduce implicit trust.
Yet in 2026, we continue to see breaches where organizations had Zero Trust deployed — and still lost control.
The uncomfortable truth is this:
Most Zero Trust failures do not come from exploits.
They come from misconfigurations.
Overly permissive policies.
Wildcard users.
Missing MFA.
Weak device posture checks.
These are silent failures — and attackers love them.
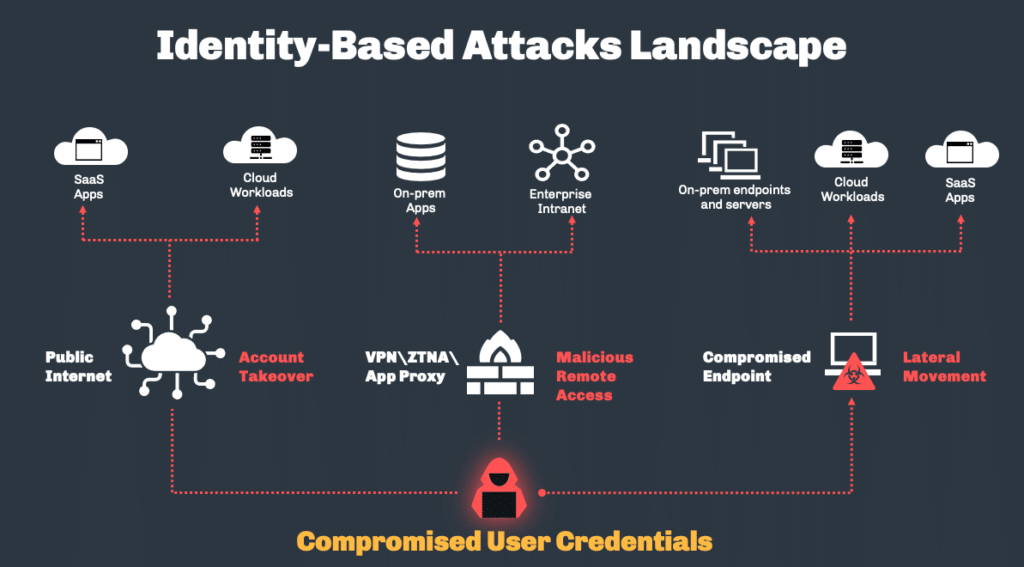
The 2026 Reality: ZTNA Has Become a Configuration Problem
4
ZTNA platforms are powerful, but they are also complex.
Modern environments often involve:
- Hundreds of access rules
- Multiple identity providers
- Device posture signals
- Geo and time-based conditions
- Risk-adaptive logic
Across vendors such as Cloudflare, Zscaler, Palo Alto Networks, and Microsoft Entra, one pattern is consistent:
A single weak rule can undermine the entire Zero Trust posture.
Why Traditional Security Reviews Miss ZTNA Weaknesses
Most organizations rely on:
- Manual reviews
- Periodic audits
- Vendor dashboards
- Checkbox compliance
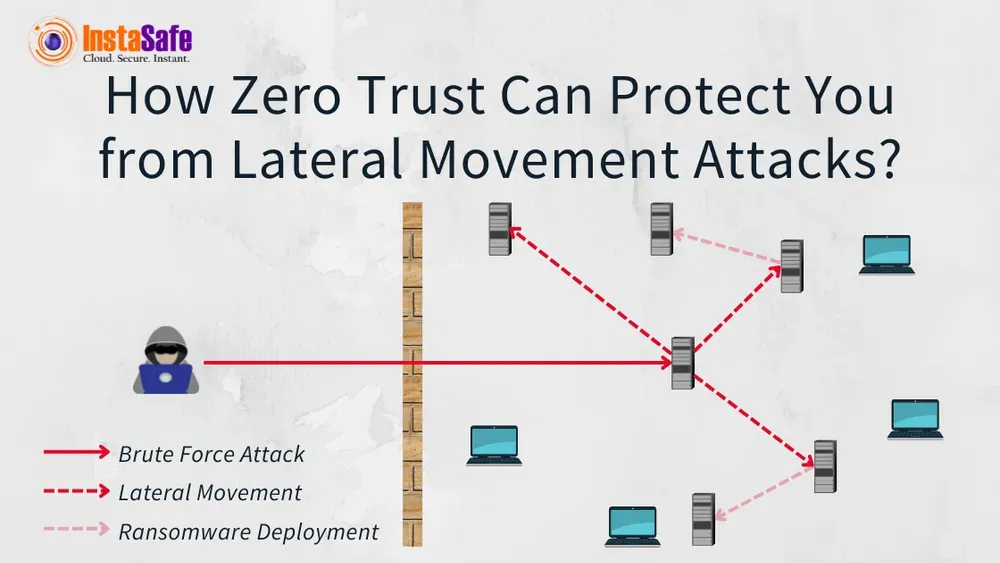
These approaches fail because they do not answer attacker-centric questions, such as:
- “Which users can reach which resources if a device is compromised?”
- “What happens if MFA is bypassed on one rule?”
- “Can a wildcard policy enable lateral movement?”
- “What does my ZTNA look like from an attacker’s perspective?”
Zero Trust needs continuous validation, not static confidence.
Introducing the CyberDudeBivash Zero-Trust Network Access Validator Scanner v2026.1


4
At CyberDudeBivash, we build tools based on how attacks actually happen — not how vendors market controls.
To address the silent failure mode of Zero Trust, we released:
CyberDudeBivash Zero-Trust Network Access Validator Scanner v2026.1
An open-source, secure-by-design ZTNA auditing and validation tool built to expose misconfigurations before attackers exploit them.
What This Tool Does (Practically, Not Theoretically)
Multi-Vendor ZTNA Parsing
The scanner understands real-world policy formats, including:
- Cloudflare Zero Trust (JSON)
- Zscaler Private Access (YAML)
- Palo Alto Prisma Access (XML)
- Generic & extensible formats for other platforms
This allows vendor-agnostic validation — a critical requirement in hybrid environments.
Misconfiguration Detection with Risk Scoring
The scanner automatically identifies:
- Wildcard users (
*) - Overly permissive resources
- Missing MFA enforcement
- Weak or absent device posture checks
- No geo or contextual restrictions
Each finding is:
- Scored (0–100)
- Classified by severity (Low → Critical)
- Paired with clear remediation guidance
Breach Path Simulation (The Eye-Opener)
Instead of listing rules, the scanner simulates access paths using attack-graph logic.
This answers:
“If an attacker compromises this identity or device, where can they go next?”
The result is a visual breach-path graph — one of the most powerful tools for:
- Architecture reviews
- Red-team exercises
- Executive risk communication
Professional Reports (Engineer & Management Friendly)
The scanner generates:
- Console findings (for engineers)
- HTML reports (for teams & audits)
- Visual attack graphs (for leadership)
No screenshots.
No spreadsheets.
Just clear, defensible security evidence.
Secure by Design: Practicing What Zero Trust Preaches
This tool itself follows Zero Trust principles:
- Explicit input validation
- No external API calls
- Least-privilege execution
- Deterministic outputs
- No hidden telemetry
If you’re validating Zero Trust, the tool doing it must be trustworthy too.
Who Should Use This Tool?
This scanner is designed for:
- Cloud Security Engineers
- IAM & Zero Trust Architects
- Blue Teams & SOC Analysts
- Red Teams validating identity attack paths
- CISOs preparing for audits
- Security consultants & MSPs
If you manage identity-based access, this tool belongs in your workflow.
Availability & Access
Free Open-Source Edition
GitHub:
https://github.com/14mb1v45h/CyberDudeBivash-Zero-Trust-Network-Access-Validator-Scanner
Includes:
- Full policy parsing
- Misconfiguration detection
- Breach path simulation
- HTML reporting
Pro & Enterprise Editions
For organizations that need scale and automation:
Pro (Individual / Teams) — $99 one-time
- Unlimited scans
- Enhanced reports
- Continuous monitoring mode
Enterprise — $499+
- Custom vendor parsers
- API integrations
- Support & customization
Contact: iambivash@cyberdudebivash.com
Final Thoughts: Zero Trust Must Be Proven, Not Assumed
Zero Trust is not something you enable once.
It is something you continuously validate.
Attackers don’t care about your architecture diagrams.
They care about the one policy that lets them in.
At CyberDudeBivash, our mission is simple:
Turn security assumptions into verifiable evidence.
Audit your ZTNA policies.
Simulate breach paths.
Fix the quiet failures – before they become headlines.
Your Cybersecurity Sentinel
Bivash Kumar Nayak
Founder, CyberDudeBivash Pvt. Ltd.
www.cyberdudebivash.com
cyberbivash.blogspot.com | cyberdudebivash-news.blogspot.com
#ZeroTrust #ZTNA #CloudSecurity #ThreatModeling #AttackGraphs #CyberDudeBivash
In 2026, Zero Trust failures rarely come from exploits.
They come from misconfigurations:
• Wildcard users
• Overly permissive resources
• Missing MFA
• Weak device posture checks
These gaps quietly enable lateral movement, privilege abuse, and data exfiltration — often without triggering alerts.
That’s why we’ve released:
CyberDudeBivash Zero-Trust Network Access Validator Scanner v2026.1
An open-source, vendor-aware ZTNA auditing tool that helps you see what attackers see.
What it does:
Parses ZTNA policies from Cloudflare, Zscaler, Prisma, Entra, Fortinet
Detects high-risk misconfigurations with risk scoring
Simulates breach paths (visual attack graphs included)
Generates clear remediation playbooks
Produces professional HTML reports for teams & audits
Free Open-Source Download:
https://github.com/14mb1v45h/CyberDudeBivash-Zero-Trust-Network-Access-Validator-Scanner
Pro / Enterprise features (PDF reports, continuous monitoring, custom vendors, integrations) are coming soon.
Early access & licensing: iambivash@cyberdudebivash.com
Zero Trust isn’t a product you buy.
It’s a posture you must continuously validate.
Don’t wait for your next “assume breach” scenario to be real.
Audit today.
What’s the biggest ZTNA challenge you’re facing right now?
#ZeroTrust #ZTNA #CloudSecurity #CyberSecurity #InfoSec #CyberDudeBivash
Leave a comment